The National Science Foundation has awarded Professor Feamster $450k over three years to develop techniques to control and prevent data leaks and the spread of malware in enterprise networks.
In Deloitte's recent Global Security Survey, nearly half of the companies surveyed reported some internal security breach; of those, about a third of breaches resulted from viruses or malware, and another third resulted from insider fraud. The Pedigree project aims to develop mechanisms to control and prevent these data breaches in enterprise networks. This growing problem begs the need for better techniques for controlling information flow in the network itself.
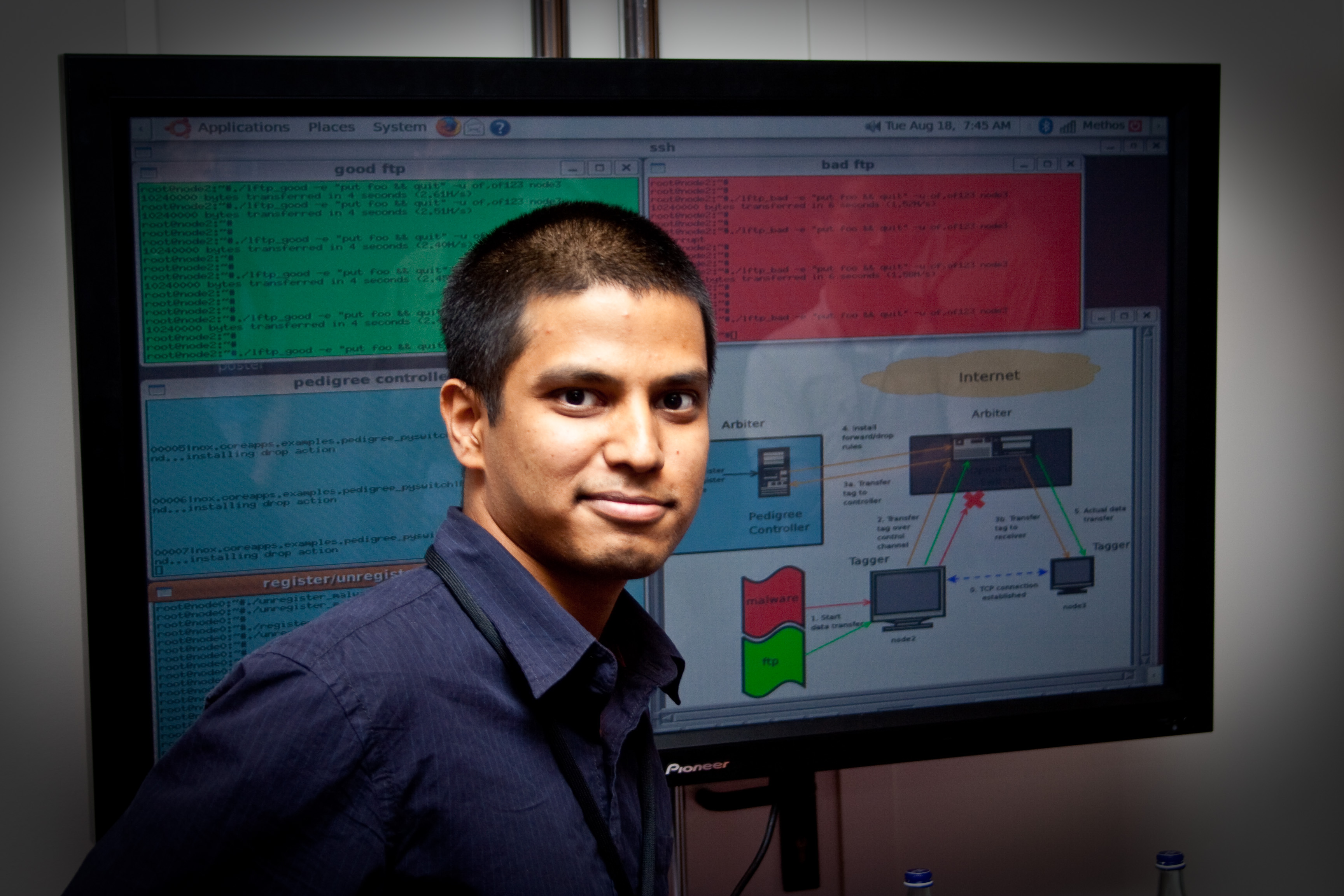
We are addressing several research challenges. First, we are exploring the appropriate granularity for tainting that preserves semantics without imposing unacceptable memory and performance overhead. Second, we are designing the system to minimize performance overhead on applications. Third, we are exploring translation mechanisms between host-based taints and network-based taints, so that taints carried in network traffic convey meaningful semantics without imposing prohibitive network overhead. The research will result in an information tracking and control system that is deployed in experimental settings (e.g., the Georgia Tech campus network) using the existing and forthcoming programmable switch implementations.
Our writeup of the system remonstration from SIGCOMM 2009 provides more details. Details on the aware are available at the NSF Web site.